Award-winning PDF software





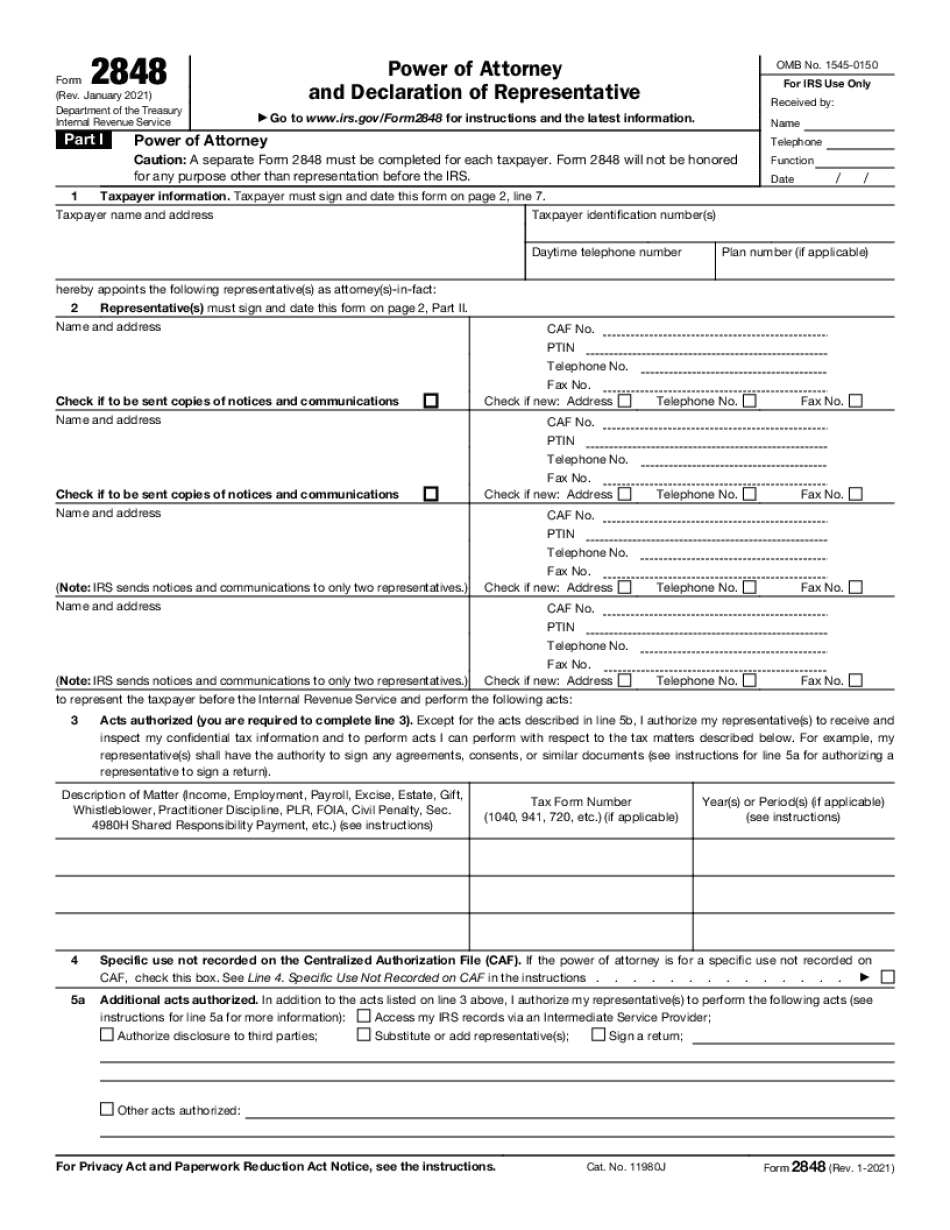
Form 2848 for Kansas City Missouri: What You Should Know
Claim Form for the Unemployment Fraud Investigation Service, if necessary, include with the complaint information received through the UI Fraud Alert System. Submit the Affidavit in Lieu of Tax Fraud to the Michigan Department of Treasury, Tax Division. The Department will investigate the case, verify the accuracy of the tax return information, and take appropriate actions against the tax evader. How Can I Protect My Personal Information from Identity Theft? Identify personal information and safeguard it against unauthorized access and use or loss. Protect your personal information with encryption and password protection. Use a secure email program to protect personal information and limit its scope. Store your most sensitive personal information in the cloud. Protect and secure online communications by encrypting all information transmission, including email. Use a password manager; enable two-factor authentication on your account; and restrict the access of your online accounts. Review your email notifications and remove those you don't need. If you don't, your information may be used to file incorrect tax returns without your knowledge. Protect your personal information by encrypting it when transmitting, storing and accessing it on the Internet. Encryption can be accomplished using a combination of encryption software, hardware security modules (HSM's), and password encryption. Hardware and software will differ in the ways they protect your information. Hardware security modules include hardware locks, password modules, software access modules, and mobile security modules. There are two main types of encryption technology that may have a security advantage. One type, known as hardware or hardware-based encryption, is most commonly used on servers, devices and networks. There are two types such as firewalls, virtual private networks (VPNs) or smart card security. Software-based encryption is more commonly used on personal computers. HSM, also known as an encrypted mobile or portable hard drive uses software to help keep your information secure. Smart cards allow for secure access to your information by using secure digital cards, software or a combination of the two. Using encryption and strong passwords on systems using software or hardware-based encryption is much safer from identity theft. Password systems are based on public or shared key and are not related to password security systems designed for businesses. Encrypting passwords are simple to implement and do not require a strong secret. Many password managers are free, and there are many programs available that will simplify these practices. Some password managers will remember and store your password for you.
Online methods assist you to arrange your doc management and supercharge the productiveness within your workflow. Go along with the short guideline to be able to complete Form 2848 for Kansas City Missouri, keep away from glitches and furnish it inside a timely method:
How to complete a Form 2848 for Kansas City Missouri?
- On the web site along with the sort, click Commence Now and go to your editor.
- Use the clues to complete the suitable fields.
- Include your personal info and contact data.
- Make certainly that you simply enter right knowledge and numbers in ideal fields.
- Carefully verify the articles from the type in addition as grammar and spelling.
- Refer to aid portion for those who have any queries or tackle our Assistance team.
- Put an digital signature on your Form 2848 for Kansas City Missouri aided by the enable of Indicator Instrument.
- Once the form is completed, push Finished.
- Distribute the all set variety by means of e-mail or fax, print it out or help save on the product.
PDF editor allows you to make adjustments with your Form 2848 for Kansas City Missouri from any world-wide-web connected equipment, personalize it in line with your requirements, indication it electronically and distribute in several methods.